The subject of mining centralization has been an important one over the previous few weeks. GHASH.io, the Bitcoin community’s largest mining pool, has for the previous month directed over 40% of the Bitcoin community’s hashpower, and two weeks in the past briefly spiked over 50%, theoretically giving it monopoly management over the Bitcoin community. Though miners quidkly left the pool and decreased its hashpower to 35%, it is clear that the issue is just not solved. On the identical time, ASICs threaten to additional centralize the very manufacturing . One strategy to fixing the issue is the one I advocated in my previous post: create a mining algorithm that’s assured to stay CPU-friendly in the long run. One other, nevertheless, is to abolish mining totally, and substitute it with a brand new mannequin for searching for consensus.
The first second contender to this point has been a technique known as “proof of stake”, the instinct behind which is as follows. In a standard proof-of-work blockchain, miners “vote” on which transactions got here at what time with their CPU energy, and the extra CPU energy you’ve gotten the proportionately bigger your affect is. In proof-of-stake, the system follows an analogous however completely different paradigm: stakeholders vote with their {dollars} (or relatively, the inner forex of the actual system). When it comes to how this works technically, the only setup is a mannequin that has been known as the “simulated mining rig”: primarily, each account has a sure likelihood per second of producing a legitimate block, very similar to a bit of mining {hardware}, and this opportunity is proportional to the account’s stability. The only components for that is:
SHA256(prevhash + handle + timestamp) <= 2^256 * stability / diff
prevhash is the hash of the earlier block, handle is the handle of the stake-miner, timestamp is the present Unix time in second, stability is the account stability of the stack-miner and diff is an adjustable international issue parameter. If a given account satisfies this equation at any explicit second, it could produce a legitimate block, giving that account some block reward.
One other strategy is to make use of not the stability, however the “coin age” (ie. the stability multiplied by the period of time that the cash haven’t been touched), because the weighting issue; this ensures extra even returns however on the expense of doubtless a lot simpler collusion assaults, since attackers have the flexibility to build up coin age, and attainable superlinearity; for these causes, I desire the plain balance-based strategy typically, and we’ll use this as our baseline for the remainder of this dialogue.
Different options to “proof of X” have been proposed, together with excellence, bandwidth, storage and id, however none are notably handy as consensus algorithms; relatively, all of those programs have most of the identical properties of proof of stake, and are thus finest carried out not directly – by making them purely mechanisms for forex distribution, after which utilizing proof of stake on these distributed cash for the precise consensus. The one exception is probably the social-graph-theory primarily based Ripple, though many cryptocurrency proponents think about such programs to be far too trust-dependent in an effort to be thought of really “decentralized”; this level might be debated, however it’s best to concentrate on one matter at a time and so we’ll concentrate on stake.
Strengths and Weaknesses
If it may be carried out appropriately, in idea proof of stake has many benefits. Specifically are three:
- It doesn’t waste any important quantity of electicity. Positive, there’s a want for stakeholders to maintain making an attempt to provide blocks, however nobody positive aspects any profit from making multiple try per account per second; therefore, the electrical energy expenditure is akin to every other non-wasteful web protocol (eg. BitTorrent)
- It could arguably present a a lot increased degree of safety. In proof of labor, assuming a liquid marketplace for computing energy the price of launching a 51% assault is the same as the price of the computing energy of the community over the course of two hours – an quantity that, by customary financial ideas, is roughly equal to the entire sum of block rewards and transaction charges supplied in two hours. In proof of stake, the brink is theoretically a lot increased: 51% of the complete provide of the forex.
- Relying on the exact algorithm in query it might probably enable for a lot sooner blockchains (eg. NXT has one block each few seconds, in comparison with one per minute for Ethereum and one per ten minutes for Bitcoin)
Observe that there’s one necessary counterargument that has been made to #2: if a big entity credibly commits to buying 51% of forex models after which utilizing these funds to repeatedly sabotage the community, then the worth will fall drastically, making it a lot simpler for that entity to puchase the tokens. This does considerably mitigate the good thing about stake, though not almost fatally; an entity that may credibly commit to buying 50% of cash is probably going additionally one that may launch 51% assaults in opposition to proof of labor.
Nevertheless, with the naive proof of stake algorithm described above, there’s one major problem: as some Bitcoin builders describe it, “there’s nothing at stake”. What meaning is that this: within the context of a proof-of-work blockchain, if there’s an unintended fork, or a deliberate transaction reversal (“double-spend”) try, and there are two competing forks of the blockchain, then miners have to decide on which one they contribute to. Their three selections are both:
- Mine on no chain and get no rewards
- Mine on chain A and get the reward if chain A wins
- Mine on chain B and get the reward if chain B wins
As I’ve commented in a previous post, observe the hanging similarity to SchellingCoin/Truthcoin right here: you win in case you go along with what everybody else goes with, besides on this case the vote is on the order of transactions, not a numerical (as in SchellingCoin) or binary (as in TruthCoin) datum. The inducement is to help the chain that everybody else helps, forcing fast convergence, and stopping profitable assaults supplied that not less than 51% of the community is just not colluding.
Within the naive proof of stake algorithm, alternatively, the alternatives of whether or not or to not vote on A and whether or not or to not vote on B are impartial; therefore, the optimum technique is to mine on any fork that you could find. Thus, in an effort to launch a profitable assault, an attacker want solely overpower all the altruists who’re prepared to vote solely on the proper chain.
The issue is, sadly, considerably basic. Proof of labor is good as a result of the property of hash verification permits the community to pay attention to one thing exterior of itself – particularly, computing energy, and that factor serves as a kind of anchor to make sure some stability. In a naive proof of stake system, nevertheless, the one factor that every chain is conscious of is itself; therefore, one can intuitively see that this makes such programs extra flimsy and fewer steady. Nevertheless, the above is merely an intuitive argument; it’s not at all a mathematical proof {that a} proof-of-stake system can’t be incentive-compatible and safe, and certainly there are a variety of potential methods to get across the subject.
The primary technique is the one that’s employed within the Slasher algorithm, and it hinges on a easy realization: though, within the case of a fork, chains aren’t conscious of something within the exterior world, they’re conscious of one another. Therefore, the best way the protocol prevents double-mining is that this: in case you mine a block, the reward is locked up for 1000 blocks, and in case you additionally mine on every other chain then anybody else can submit the block from the opposite chain into the unique chain in an effort to steal the mining reward. Observe, nevertheless, that issues aren’t fairly so easy, and there’s one catch: the miners need to be recognized upfront. The issue is that if the algorithm given above is used straight, then the problem arises that, utilizing a probabilistic technique, double mining turns into very straightforward to cover.
The problem is that this: suppose that you’ve 1% stake, and thus each block there’s a 1% likelihood that it is possible for you to to provide (hereinafter, “signal”) it. Now, suppose there’s a fork between chain A and chain B, with chain A being the “right” chain. The “sincere” technique is to attempt to generate blocks simply on A, getting an anticipated 0.01 A-coins per block. An alternate technique, nevertheless, is to attempt to generate blocks on each A and B, and in case you discover a block on each on the identical time then discarding B. The payout per block is one A-coin in case you get fortunate on A (0.99% likelihood), one B-coin in case you get fortunate on B (0.99% likelihood) and one A-coin, however no B-coins, in case you get fortunate on each; therefore, the anticipated payout is 0.01 A-coins plus 0.0099 B-coins in case you double-vote. If the stakeholders that have to signal a specific block are determined upfront, nevertheless (ie. particularly, determined earlier than a fork begins), then there isn’t a risk of getting the chance to vote on A however not B; you both have the chance on each or neither. Therefore, the “dishonest” technique merely collapses into being the identical factor because the “sincere” technique.
The Block Signer Choice Downside
However then if block signers are determined upfront, one other subject arises: if accomplished mistaken, block signers may “mine” their blocks, repeatedly making an attempt to create a block with completely different random knowledge till the ensuing block triggers that very same signer having the privilege to signal a block once more very quickly. For instance, if the signer for block N+1000 was merely chosen from the hash of block N, and an attacker had 1% stake, then the attacker may maintain rebuilding the block till block N+1000 additionally had the attacker as its signer (ie. an anticipated 100 iterations). Over time, the attacker would naturally acquire signing privilege on different blocks, and thus ultimately come to fully saturate the blockchain with length-1000 cycles managed by himself. Even when the hash of 100 blocks put collectively is used, it is attainable to govern the worth. Thus, the query is, how will we decide what the signers for future blocks are going to be?
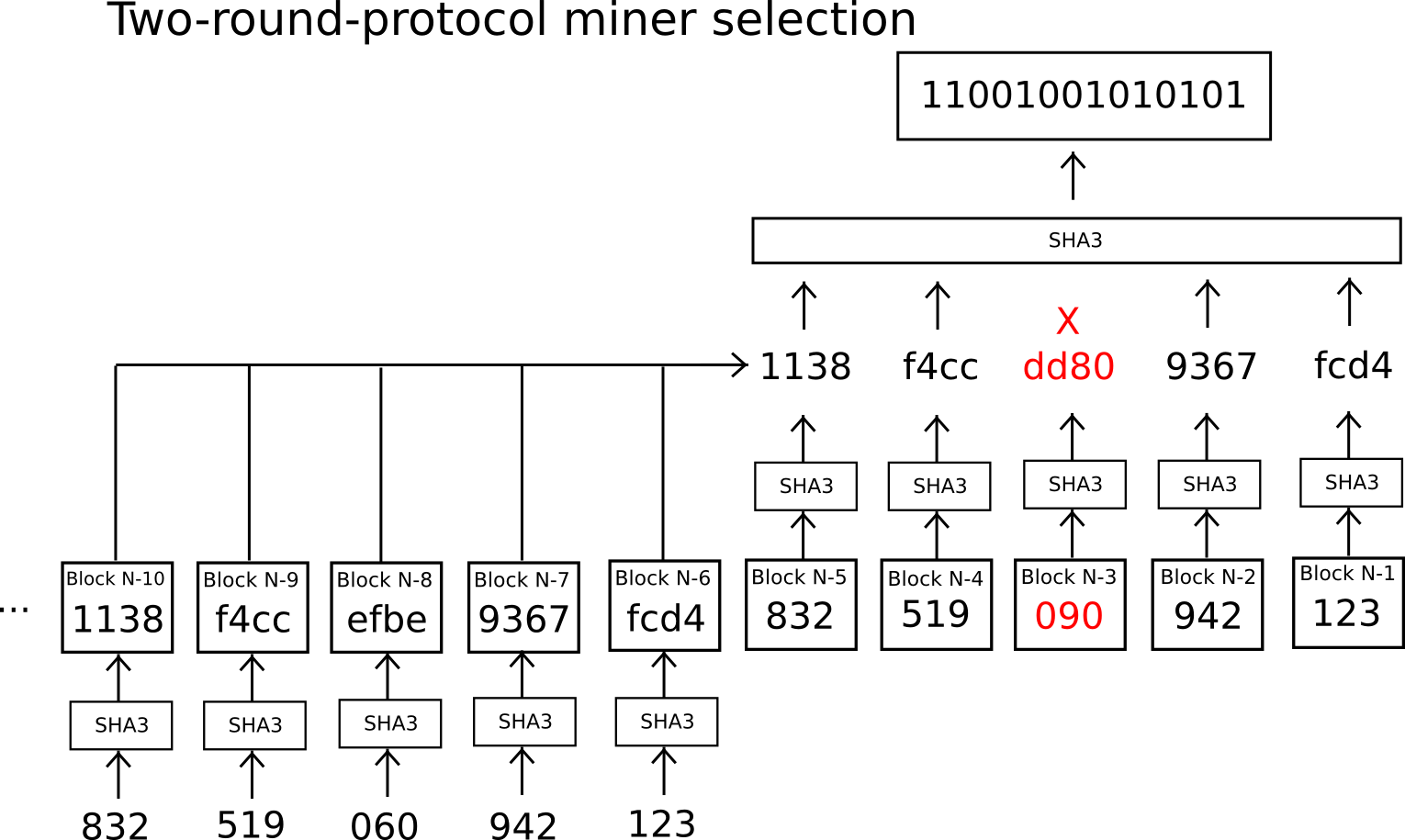
The answer utilized in Slasher is to make use of a safe decentralized random quantity generator protocol: many events are available in, first undergo the blockchain the hashes of their values, after which submit their values. There is no such thing as a likelihood of manipulation this fashion, as a result of every submitter is certain to submit within the second spherical the worth whose hash they supplied within the first spherical, and within the first spherical nobody has sufficient data in an effort to have interaction in any manipulation. The participant nonetheless has a selection of whether or not or to not take part within the second spherical, however the two countervailing factors are that (1) this is just one little bit of freedom, though it turns into better for big miners that may management a number of accounts, and (2) we will institute a rule that failing to take part causes forfeiture of 1’s mining privilege (miners in spherical N select miners for spherical N+1 throughout spherical N-1, so there is a chance to do that if sure round-N miners misbehave throughout this choice step).
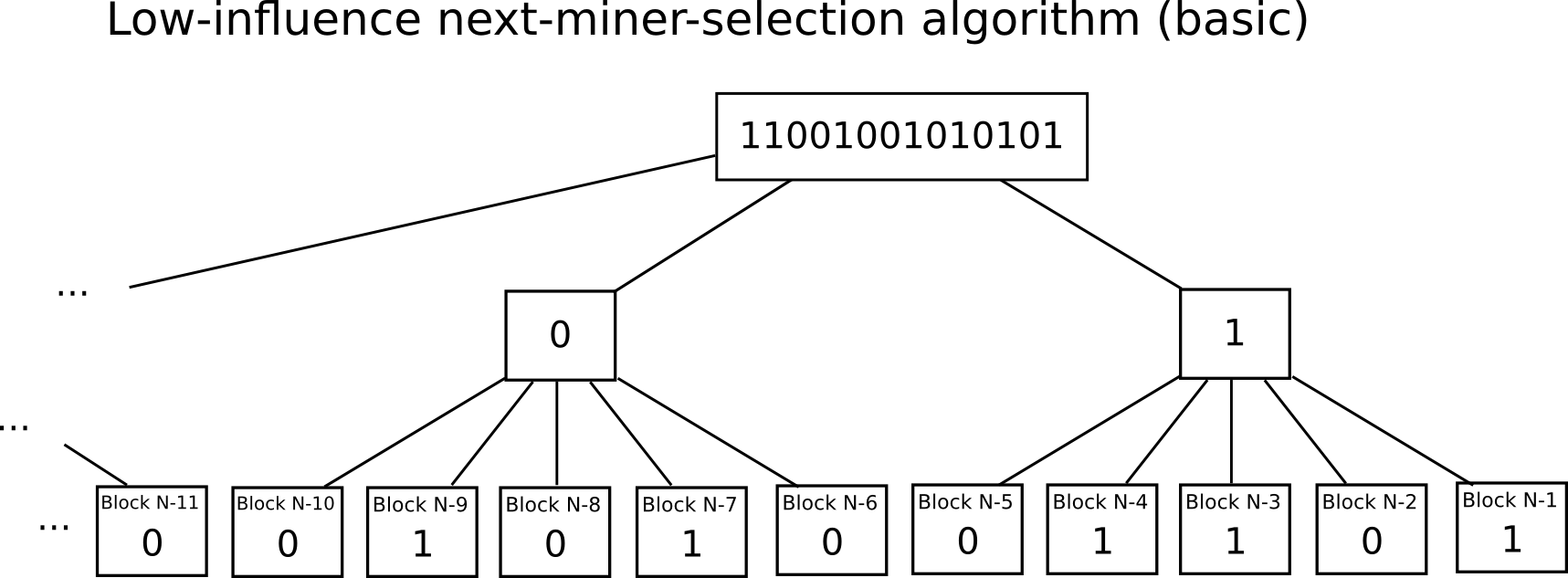
One other thought, proposed by Iddo Bentov and others of their “Cryptocurrencies Without Proof of Work” paper, is to make use of one thing known as a “low-influence” operate – primarily, a operate such that there’s solely a really low likelihood {that a} single actor will be capable to change the outcome by altering the enter. A easy instance of an LIF over small units is majority rule; right here, as a result of we try to choose a random miner, we’ve a really massive set of choices to select from, so majority rule per bit is used (eg. in case you have 500 events and also you wish to decide a random miner out of a billion, assign them into thirty teams of 17, and have every group vote on whether or not their explicit bit is zero or one, after which recombine the bits as a binary quantity on the finish). This removes the necessity for a sophisticated two-step protocol, permitting it to probably be accomplished way more shortly and even in parallel, lowering the chance that the pre-chosen stake-miners for some explicit block will get collectively and collude.
A 3rd attention-grabbing technique, utilized by NXT, is to make use of the addresses of the stake-miners for blocks N and N+1 to decide on the miner for block N+2; this by definition provides just one selection for the subsequent miner in every block. Including a criterion that each miner must be locked in for 1440 blocks in an effort to take part prevents sending transactions as a type of double-mining. Nevertheless, having such fast stake-miner choice additionally compromises the nothing-at-stake resistance property because of the probabilistic double-mining downside; that is the explanation why intelligent schemes to make miner dedication occur in a short time are finally, past a sure level, undesirable.
Lengthy-Vary Assaults
Whereas the Slasher strategy does successfully remedy the nothing-at-stake downside in opposition to conventional 51% assaults, an issue arises within the case of one thing known as a “long-range assault”: as an alternative of an attacker beginning mining from ten blocks earlier than the present block, the attacker begins ten thousand blocks in the past. In a proof-of-work context, that is foolish; it principally means doing hundreds of instances as a lot work as is critical to launch an assault. Right here, nevertheless, making a block is sort of computationally free, so it is a affordable technique. The explanation why it really works is that Slasher’s course of for punishing multi-mining solely lasts for 1000 blocks, and its course of for figuring out new miners lasts 3000 blocks, so exterior the “scope” of that vary Slasher features precisely just like the naive proof-of-stake coin. Observe that Slasher continues to be a considerable enchancment; actually, assuming customers by no means change it may be made absolutely safe by introducing a rule into every shopper to not settle for forks going again greater than 1000 blocks. The issue is, nevertheless, what occurs when a brand new person enters the image.
When a brand new person downloads a proof-of-stake-coin shopper for the primary time, it’ll see a number of variations of the blockchain: the longest, and subsequently reliable, fork, and plenty of pretenders making an attempt to mine their very own chains from the genesis. As described above, proof-of-stake chains are fully self-referential; therefore, the shopper seeing all of those chains has no thought about any surrounding context like which chain got here first or which has extra worth (observe: in a hybrid proof-of-stake plus social graph system, the person would get preliminary blockchain knowledge from a trusted supply; this strategy is affordable, however is just not absolutely decentralized). The one factor that the shopper can see is the allocation within the genesis block, and all the transactions since that time. Thus, all “pure” proof-of-stake programs are finally everlasting nobilities the place the members of the genesis block allocation all the time have the final word say. It doesn’t matter what occurs ten million blocks down the highway, the genesis block members can all the time come collectively and launch an alternate fork with an alternate transaction historical past and have that fork take over.
Should you perceive this, and you’re nonetheless okay with pure proof of stake as an idea (the precise motive why you would possibly nonetheless be okay is that, if the preliminary issuance is completed proper, the “the Aristocracy” ought to nonetheless be massive sufficient that it can not virtually collude), then the conclusion permits for some extra imaginative instructions when it comes to how proof of stake can play out. The only thought is to have the members of the genesis block vote on each block, the place double-mining is punished by everlasting lack of voting energy. Observe that this method really solves nothing-at-stake points fully, since each genesis block holder has a mining privilege that has worth perpetually into the longer term, so it’ll all the time not be value it to double-mine. This technique, nevertheless, has a finite lifespan – particularly, the utmost life (and curiosity) span of the genesis signers, and it additionally provides the the Aristocracy a everlasting profit-making privilege, and never simply voting rights; nevertheless, nonetheless the existence of the algorithm is encouraging as a result of it means that long-range-nothing-at-stake could be essentially resolvable. Thus, the problem is to determine a way to verify voting privileges switch over, whereas nonetheless on the identical time sustaining safety.
Altering Incentives
One other strategy to fixing nothing-at-stake comes on the downside from a totally completely different angle. The core downside is, in naive proof-of-stake, rational people will double-vote. The Slasher-like options all attempt to remedy the issue by making it not possible to double-vote, or on the very least closely punishing such a technique. However what if there’s one other strategy; particularly, what if we as an alternative take away the inducement to take action? In all the proof of stake programs that I described above, the inducement is apparent, and sadly basic: as a result of whoever is producing blocks wants an incentive to take part within the course of, they profit in the event that they embody a block in as many forks as attainable. The answer to this conundrum comes from an imaginative, out-of-the-box proposal from Daniel Larimer: transactions as proof of stake.
The core thought behind transactions as proof-of-stake is straightforward: as an alternative of mining being accomplished by a separate class of people, whether or not pc {hardware} house owners or stakeholders, mining and transaction sending are merged into one. The naive TaPoS algorithm is as follows:
- Each transaction should comprise a reference (ie. hash) to the earlier transaction
- A candidate state-of-the-system is obtained by calculating the results of a ensuing transaction chain
- The right chain amongst a number of candidates is the one which has both (i) the longest coin-days-destroyed (ie. variety of cash within the account * time since final entry), or (ii) the very best transaction charges (these are two completely different choices that we are going to analyze individually)
This algorithm has the property that this can be very unscalable, breaking down past about 1 transaction per 2-5 seconds, and it isn’t the one which Larimer suggests or the one that can really be used; relatively, it is merely a proof of idea that we are going to analyze to see if this strategy is legitimate in any respect. Whether it is, then there are possible methods to optimize it.
Now, let’s examine what the economics of this are. Suppose that there’s a fork, and there are two competing variations of the TaPoS chain. You, as a transaction sender, made a transaction on chain A, and there’s now an upcoming chain B. Do you’ve gotten the inducement to double-mine and embody your transaction in chain B as properly? The reply is not any – actually you really wish to double-spend your recipient so you wouldn’t put the transaction on one other chain. This argument is very potent within the case of long-range assaults, the place you already acquired your product in trade for the funds; within the brief time period, after all, the inducement nonetheless exists to verify the transaction is distributed, so senders do have the inducement to double-mine; nevertheless, as a result of the fear is strictly time-limited this may be resolved through a Slasher-like mechanism.
One concern is that this: given the presence of forks, how straightforward is it to overwhelm the system? If, for instance, there’s a fork, and one explicit entity desires to double-spend, below what circumstances is that attainable? Within the transaction-fee model, the requirement is fairly easy: you’ll want to spend extra txfees than the remainder of the community. This appears weak, however in actuality it is not; we all know that within the case of Bitcoin, as soon as the forex provide stops growing mining will rely solely on transaction charges, and the mechanics are precisely the identical (for the reason that quantity that the community will spend on mining will roughly correspond to the entire variety of txfees being despatched in); therefore, fee-based TaPoS is on this regard not less than as safe as fee-only PoW mining. Within the second case, we’ve a unique mannequin: as an alternative of mining along with your cash, you’re mining along with your liquidity. Anybody can 51% assault the system if and provided that they’ve a sufficiently massive amount of coin-days-destroyed on them. Therefore, the price of spending a big txfee after the actual fact is changed by the price of sacrificing liquidity earlier than the actual fact.
Price of Liquidity
The dialogue round liquidity results in one other necessary philosophical level: safety can’t be cost-free. In any system the place there’s a block reward, the factor that’s the prerequisite for the reward (whether or not CPU, stake, or one thing else) can’t be free, since in any other case everybody could be claiming the reward at infinitum, and in TaPoS transaction senders should be offering some type of charge to justify safety. Moreover, no matter useful resource is used to again the safety, whether or not CPU, forex sacrifices or liquidity sacrifices, the attacker want solely get their palms on the same amount of that useful resource than the remainder of the community. Observe that, within the case of liquidity sacrifices (which is what naive proof of stake is), the related amount right here is definitely not 50% of cash, however relatively the privilege of accessing 50% of cash for just a few hours – a service that, assuming a superbly environment friendly market, would possibly solely price just a few hundred thousand {dollars}.
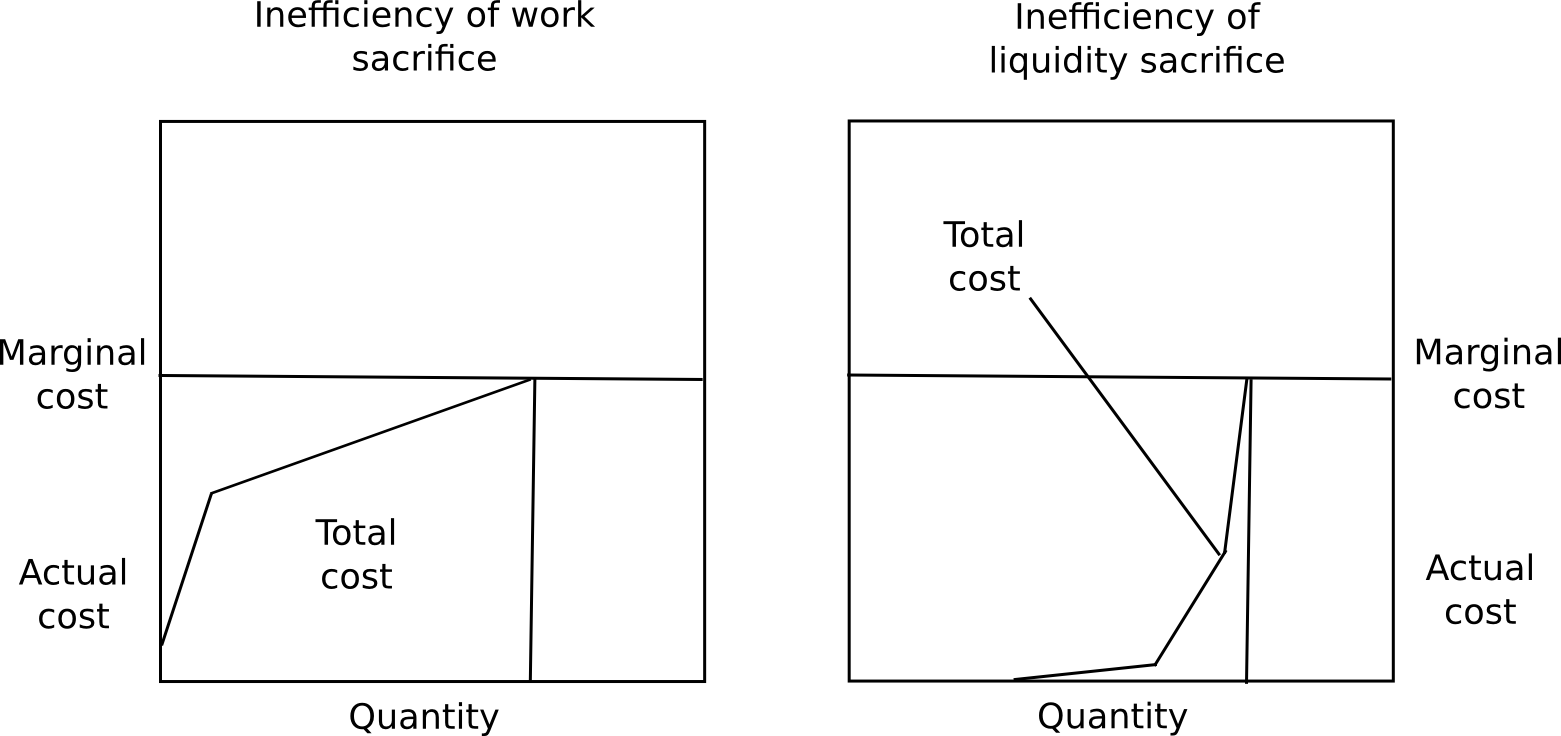
The answer to this puzzle is that marginal price is just not the identical factor as common price. Within the case of proof of labor, that is true solely to a really restricted extent; though miners do earn a constructive nonzero revenue from mining, all of them pay a excessive price (except they’re CPU miners heating their houses, however even there there are substantial effectivity losses; laptops working hash features at 100%, although efficient at heating, are essentially much less efficient than programs designed for the duty). Within the case of forex sacrifices, everybody pays the identical, however the fee is redistributed as a dividend to everybody else, and this revenue is simply too dispersed to be recovered through market mechanisms; thus, though the system is expensive from an area perspective, it’s costless from a worldwide perspective.
The final choice, liquidity sacrifice, is in between the 2. Though liquidity sacrifice is expensive, there’s a substantial quantity of disparity in how a lot folks worth liquidity. Some folks, like particular person customers or companies with low financial savings, closely worth liquidity; others, like savers, don’t worth liquidity in any respect (eg. I couldn’t care much less if I misplaced the flexibility to spend ten of my bitcoins for some length). Therefore, though the marginal price of liquidity will likely be excessive (particularly, essentially equal to both the mining reward or the transaction charge), the typical price is far decrease. Therefore, there’s a leverage impact that permits the price of an assault to be a lot increased than the inefficiency of the community, or the quantity that senders spend on txfees. Moreover, observe that in Larimer’s scheme particularly, issues are rigged in such a a approach that all liquidity that’s sacrificed in consensus is liquidity that was being sacrificed anyway (particularly, by not sending cash earlier), so the sensible degree of inefficiency is zero.
Now, TaPoS does have its issues. First, if we attempt to make it extra scalable by reintroducing the idea of blocks, then there ideally must be some motive to provide blocks that isn’t revenue, in order to not reintroduce the nothing-at-stake downside. One strategy could also be to drive a sure class of enormous transaction senders to create blocks. Second, attacking a sequence continues to be theoretically “cost-free”, so the safety assurances are considerably much less good than they’re in proof-of-work. Third, within the context of a extra sophisticated blockchain like Ethereum, and never a forex, some transactions (eg. finalizing a guess) are literally worthwhile to ship, so there will likely be incentive to double-mine on not less than some transactions (although not almost all, so there’s nonetheless some safety). Lastly, it is a genesis-block-nobility system, similar to all proof-of-stake essentially is. Nevertheless, so far as pure proof-of-stake programs go, it does appear a a lot better spine than the model of proof of stake that emulated Bitcoin mining.
Hybrid Proof of Stake
Given the attractiveness of proof of stake as an answer for growing effectivity and safety, and its simultaneous deficiencies when it comes to zero-cost assaults, one reasonable answer that has been introduced up many instances is hybrid proof of stake, in its newest incantation known as “proof of activity“. The concept behind proof of exercise is straightforward: blocks are produced through proof of labor, however each block randomly assigns three stakeholders that have to signal it. The subsequent block can solely be legitimate as soon as these signatures are in place. On this system, in idea, an attacker with 10% stake would see 999 of his 1000 blocks not being signed, whereas within the reliable community 729 out of 1000 blocks could be signed; therefore, such an attacker could be penalized in mining by an element of 729.
Nevertheless, there’s a downside: what motivates signers to signal blocks on just one chain? If the arguments in opposition to pure proof of stake are right, then most rational stake-miners would signal each chains. Therefore, in hybrid PoS, if the attacker indicators solely his chain, and altruists solely signal the reliable chain, and everybody else indicators each, then if the attacker can overpower the altruists on the stake entrance that signifies that the attacker can overtake the chain with lower than a 51% assault on the mining entrance. If we belief that altruists as a gaggle are extra highly effective in stake than any attacker, however we do not belief that an excessive amount of, then hybrid PoS looks as if an affordable hedge choice; nevertheless, given the reasoning above, if we wish to hybridize one would possibly ask if hybrid PoW + TaPoS may not be the extra optimum approach to go. For instance, one may think about a system the place transactions have to reference latest blocks, and a blockchain’s rating is calculated primarily based on proof of labor and coin-days-destroyed counts.
Conclusion
Will we see proof of stake emerge as a viable various to proof of labor within the subsequent few years? It might be. From a pure effectivity perspective, if Bitcoin, or Ethereum, or every other PoW-based platform get to the purpose the place they’ve related market cap to gold, silver, the USD, EUR or CNY, or every other mainstream asset, then over 100 billion {dollars} value of recent forex models will likely be produced per yr. Underneath a pure-PoW regime, an quantity of financial energy approaching that will likely be spent on hashing yearly. Thus, the fee to society of sustaining a proof-of-work cryptocurrency is about the identical as the price of sustaining the Russian army (the analogy is especially potent as a result of militaries are additionally proof of labor; their solely worth to anybody is defending in opposition to different militaries). Underneath hybrid-PoS, which may safely be dropped to $30 billion per yr, and below pure PoS it might be nearly nothing, besides relying on implementation perhaps just a few billion {dollars} of price from misplaced liquidity.
Finally, this boils right down to a philosophical query: precisely how a lot does decentralization imply to us, and the way a lot are we prepared to pay for it? Keep in mind that centralized databases, and even quasi-centralized ones primarily based on Ripple consensus, are free. If excellent decentralization is certainly value 100 billion price ticket, then we must always simply centralize and let just a few governments run the databases. But when we’ve a stable, viable proof of stake algorithm, then we’ve a 3rd choice: a system which is each decentralized and cost-free (observe that helpful proof of labor additionally matches this criterion, and could also be simpler); in that case, the dichotomy doesn’t exist in any respect and decentralization turns into the apparent selection.
