Particular because of Andrew Miller for arising with this assault, and to Zack Hess, Vlad Zamfir and Paul Sztorc for dialogue and responses
One of many extra fascinating surprises in cryptoeconomics in current weeks got here from an assault on SchellingCoin conceived by Andrew Miller earlier this month. Though it has all the time been understood that SchellingCoin, and comparable techniques (together with the extra superior Truthcoin consensus), depend on what’s up to now a brand new and untested cryptoeconomic safety assumption – that one can safely depend on folks performing actually in a simultaneous consensus sport simply because they consider that everybody else will – the issues which were raised up to now need to do with comparatively marginal points like an attacker’s potential to exert small however growing quantities of affect on the output over time by making use of continued stress. This assault, then again, reveals a way more elementary downside.
The state of affairs is described as follows. Suppose that there exists a easy Schelling sport the place customers vote on whether or not or not some explicit truth is true (1) or false (0); say in our instance that it is really false. Every person can both vote 1 or 0. If a person votes the identical as the bulk, they get a reward of P; in any other case they get 0. Thus, the payoff matrix seems as follows:
| You vote 0 | You vote 1 | |
| Others vote 0 | P | 0 |
| Others vote 1 | 0 | P |
The idea is that if everybody expects everybody else to vote in truth, then their incentive is to additionally vote in truth with the intention to adjust to the bulk, and that is the explanation why one can anticipate others to vote in truth within the first place; a self-reinforcing Nash equilibrium.
Now, the assault. Suppose that the attacker credibly commits (eg. through an Ethereum contract, by merely placing one’s repute at stake, or by leveraging the repute of a trusted escrow supplier) to pay out X to voters who voted 1 after the sport is over, the place X = P + ε if the bulk votes 0, and X = 0 if the bulk votes 1. Now, the payoff matrix seems like this:
| You vote 0 | You vote 1 | |
| Others vote 0 | P | P + ε |
| Others vote 1 | 0 | P |
Thus, it is a dominant technique for anybody to vote 1 it doesn’t matter what you assume the bulk will do. Therefore, assuming the system isn’t dominated by altruists, the bulk will vote 1, and so the attacker is not going to have to pay something in any respect. The assault has efficiently managed to take over the mechanism at zero value. Observe that this differs from Nicholas Houy’s argument about zero-cost 51% attacks on proof of stake (an argument technically extensible to ASIC-based proof of labor) in that right here no epistemic takeover is required; even when everybody stays useless set in a conviction that the attacker goes to fail, their incentive continues to be to vote to assist the attacker, as a result of the attacker takes on the failure danger themselves.
Salvaging Schelling Schemes
There are a couple of avenues that one can take to attempt to salvage the Schelling mechanism. One strategy is that as an alternative of spherical N of the Schelling consensus itself deciding who will get rewarded based mostly on the “majority is correct” precept, we use spherical N + 1 to find out who needs to be rewarded throughout spherical N, with the default equilibrium being that solely individuals who voted appropriately throughout spherical N (each on the precise truth in query and on who needs to be rewarded in spherical N – 1) needs to be rewarded. Theoretically, this requires an attacker wishing to carry out a cost-free assault to deprave not only one spherical, but in addition all future rounds, making the required capital deposit that the attacker should make unbounded.
Nonetheless, this strategy has two flaws. First, the mechanism is fragile: if the attacker manages to deprave some spherical within the far future by really paying up P + ε to everybody, no matter who wins, then the expectation of that corrupted spherical causes an incentive to cooperate with the attacker to back-propagate to all earlier rounds. Therefore, corrupting one spherical is dear, however corrupting 1000’s of rounds isn’t rather more pricey.
Second, due to discounting, the required deposit to beat the scheme doesn’t must be infinite; it simply must be very very massive (ie. inversely proportional to the prevailing rate of interest). But when all we would like is to make the minimal required bribe bigger, then there exists a a lot less complicated and higher technique for doing so, pioneered by Paul Storcz: require contributors to place down a big deposit, and construct in a mechanism by which the extra competition there may be, the extra funds are at stake. On the restrict, the place barely over 50% of votes are in favor of 1 final result and 50% in favor of the opposite, the complete deposit it taken away from minority voters. This ensures that the assault nonetheless works, however the bribe should now be larger than the deposit (roughly equal to the payout divided by the discounting price, giving us equal efficiency to the infinite-round sport) fairly than simply the payout for every spherical. Therefore, with the intention to overcome such a mechanism, one would wish to have the ability to show that one is able to pulling off a 51% assault, and maybe we might merely be comfy with assuming that attackers of that measurement don’t exist.
One other strategy is to depend on counter-coordination; basically, someway coordinate, maybe through credible commitments, on voting A (if A is the reality) with chance 0.6 and B with chance 0.4, the speculation being that it will permit customers to (probabilistically) declare the mechanism’s reward and a portion of the attacker’s bribe on the identical time. This (appears to) work significantly nicely in video games the place as an alternative of paying out a continuing reward to every majority-compliant voter, the sport is structured to have a continuing complete payoff, adjusting particular person payoffs to perform this objective is required. In such conditions, from a collective-rationality standpoint it’s certainly the case that the group earns a highest revenue by having 49% of its members vote B to assert the attacker’s reward and 51% vote A to verify the attacker’s reward is paid out.
Nonetheless, this strategy itself suffers from the flaw that, if the attacker’s bribe is excessive sufficient, even from there one can defect. The elemental downside is that given a probabilistic combined technique between A and B, for every the return all the time modifications (nearly) linearly with the chance parameter. Therefore, if, for the person, it makes extra sense to vote for B than for A, it should additionally make extra sense to vote with chance 0.51 for B than with chance 0.49 for B, and voting with chance 1 for B will work even higher.
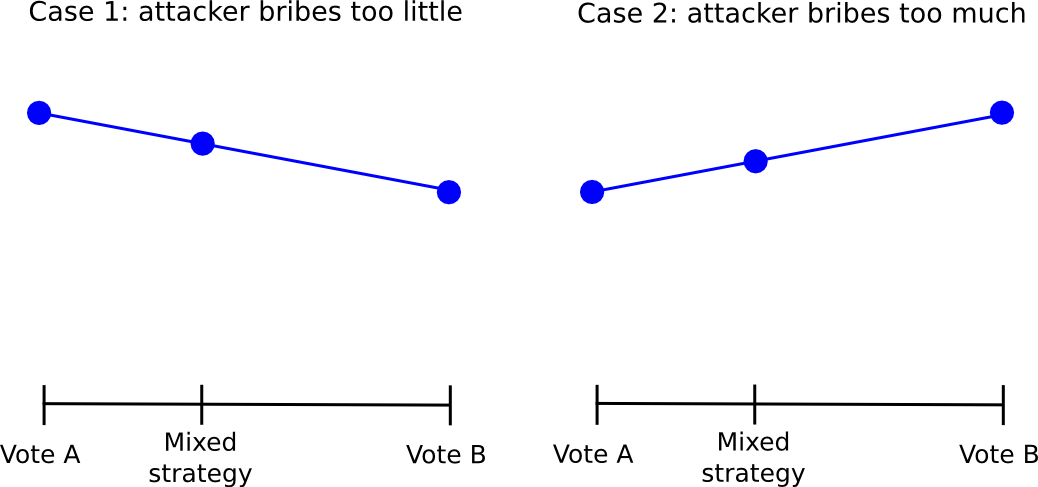
Therefore, everybody will defect from the “49% for 1” technique by merely all the time voting for 1, and so 1 will win and the attacker can have succeeded within the costless takeover. The truth that such sophisticated schemes exist, and are available so near “seeming to work” means that maybe within the close to future some complicated counter-coordination scheme will emerge that really does work; nevertheless, we have to be ready for the eventuality that no such scheme might be developed.
Additional Penalties
Given the sheer variety of cryptoeconomic mechanisms that SchellingCoin makes potential, and the significance of such schemes in almost all purely “trust-free” makes an attempt to forge any sort of hyperlink between the cryptographic world and the true world, this assault poses a possible critical menace – though, as we are going to later see, Schelling schemes as a class are finally partially salvageable. Nonetheless, what’s extra fascinating is the a lot bigger class of mechanisms that do not look fairly like SchellingCoin at first look, however the truth is have very comparable units of strengths and weaknesses.
Notably, allow us to level to at least one very particular instance: proof of labor. Proof of labor is the truth is a multi-equilibrium sport in a lot the identical method that Schelling schemes are: if there exist two forks, A and B, then if you happen to mine on the fork that finally ends up successful you get 25 BTC and if you happen to mine on the fork that finally ends up shedding you get nothing.
| You mine on A | You mine on B | |
| Others mine on A | 25 | 0 |
| Others mine on B | 0 | 25 |
Now, suppose that an attacker launches a double-spend assault in opposition to many events concurrently (this requirement ensures that there isn’t a single celebration with very sturdy incentive to oppose the attacker, opposition as an alternative turning into a public good; alternatively the double spend could possibly be purely an try and crash the value with the attacker shorting at 10x leverage), and name the “essential” chain A and the attacker’s new double-spend fork B. By default, everybody expects A to win. Nonetheless, the attacker credibly commits to paying out 25.01 BTC to everybody who mines on B if B finally ends up shedding. Therefore, the payoff matrix turns into:
| You mine on A | You mine on B | |
| Others mine on A | 25 | 25.01 |
| Others mine on B | 0 | 25 |
Thus, mining on B is a dominant technique no matter one’s epistemic beliefs, and so everybody mines on B, and so the attacker wins and pays out nothing in any respect. Notably, observe that in proof of labor we don’t have deposits, so the extent of bribe required is proportional solely to the mining reward multiplied by the fork size, not the capital value of 51% of all mining tools. Therefore, from a cryptoeconomic safety standpoint, one can in some sense say that proof of labor has nearly no cryptoeconomic safety margin in any respect (if you’re uninterested in opponents of proof of stake pointing you to this article by Andrew Poelstra, be at liberty to hyperlink them right here in response). If one is genuinely uncomfortable with the weak subjectivity situation of pure proof of stake, then it follows that the proper resolution might maybe be to enhance proof of labor with hybrid proof of stake by including safety deposits and double-voting-penalties to mining.
After all, in observe, proof of labor has survived regardless of this flaw, and certainly it might proceed to outlive for a very long time nonetheless; it might simply be the case that there is a excessive sufficient diploma of altruism that attackers are usually not really 100% satisfied that they may succeed – however then, if we’re allowed to depend on altruism, naive proof of stake works nice too. Therefore, Schelling schemes too might nicely merely find yourself working in observe, even when they aren’t completely sound in concept.
The following a part of this publish will talk about the idea of “subjective” mechanisms in additional element, and the way they can be utilized to theoretically get round a few of these issues.
